[web] Update getSignedIdentityKeysBlobSelector to await initOlm();
Summary:
Once I added cryptoStore to the redux-persist "whitelist," I noticed that refreshing the page caused an error. The error had to do with olm.Account() not being a constructor. After looking into it, I realized that the issue was that we weren't awaiting initOlm in getSignedIdentityKeysBlobSelector before trying to use olm functions.
Why wasn't this an issue before?
Previously, the only places on web where we were using olm were LoginForm, TraditionalLoginForm, and SIWELoginForm.
In all of those places we made sure that await initOlm had completed prior to using any olm functionality (either explicitly in LoginForm, or implicitly in the child TraditionalLoginForm and SIWELoginForm components) so this was never an issue.
I failed to ensure that we were handling await initOlm() when writing getSignedIdentityKeysBlobSelector. This caused a crash on refresh because the olm codepaths in getSignedIdentityKeysBlobSelector get "hit" immediately as part of Socket "rendering."
The reason I wasn't catching this previously is
A. I either had OLM initialized after authing in... so things worked.
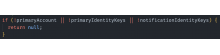
B. primaryAccount/primaryIdentityKeys/notificationIdentityKeys were unset because they weren't persisted, and getSignedIdentityKeysBlobSelector early returned:
... so things worked.
Once I added cryptoStore to redux-persist, I ran into the situation where
A. OLM hadn't been initialized.
B. getSignedIdentityKeysBlobSelector was getting past the early return case... and the new olm.Account() call failed.
In this diff I add await initOlm() to getSignedIdentityKeysBlobSelector and make the necessary modifications in TraditionalLoginForm and SIWELoginForm to accomodate the changes.
Test Plan:
- Made sure that I could log in via TraditionalLoginForm and set breakpoints on the keyserver side to ensure we got what we expect for signedIdentityKeysBlob
- Made sure that I could log in via SIWELoginForm and set breakpoints on the keyserver side to ensure we got what we expect for signedIdentityKeysBlob
- I patched in the commit where I add cryptoStore to the redux-persist "whitelist" and ensure that things are as expected when I refresh the page.
- I remove signedIdentityKeysBlob from the signed_identity_keys cookies table and test that it get repopulated via SIGNED_IDENTITY_KEYS_BLOB request by:
A. Killing keyserver and restarting it, checking that web sends back response with signedIdentityKeysBlob and DB gets updated
B. Refreshing weband checking that keyserver sent SIGNED_IDENTITY_KEYS_BLOB request and web responded with correct signedIdentityKeysBlob response and DB got updated
Reviewers: ashoat, marcin, michal
Reviewed By: ashoat
Subscribers: tomek
Differential Revision: https://phab.comm.dev/D7081